Many Ugandans use SIM cards in their smart and feature phones, but never really know what purposes the SIM card offers, like security and how it can be helpful to them, so today here at Tech point Mag, we are going to be taking you through what a SIM card is : so what’s a SIM card?
A Subscriber Identity Module (SIM) card is a chip inside most modern cellular phones that stores information your phone needs to communicate with your carrier’s cell towers. SIM cards come in different sizes and if you were to remove the SIM card from your phone you wouldn’t be able to text, call, or access anything on the internet.

What Is A SIM Card?
Believe it or not, SIM cards have been on the scene since 1991. They were first developed by a German manufacturer for a Finnish mobile carrier. Billions of SIM cards have been sold to date.
SIM cards are mandatory for phones connecting to the Global System for Mobile communications (GSM) networks, which is the telecommunications standard in over 193 countries that stores identification and security data on the card.
A SIM card is a small smart card made up of embedded contacts and semiconductors that has gone through four sizes over the years:
- Full-Size (1FF or 1st Form Factor) was the size of a credit card; 85.6 mm x 53.98 mm.
- Mini-SIM (2FF) was drastically smaller coming in at 25 mm x 15 mm first being used in 1996.
- Micro-SIM (3FF) made improvements in length with measurements of 15 mm x 12 mm.
- Nano-SIM (4FF) is the most recent form and is 12.3 mm x 8.8 mm.
As phones got smaller and thinner, the need for smaller components inside became more apparent. Having a card the size of a credit card inside a device the same size wasn’t realistic. Nowadays, SIM cards have been stripped down, removing almost all the surrounding plastic, and are essentially just a small chip.
The next-generation SIM technology is called an Embedded-SIM (eSIM). It’s a non-replaceable chip soldered directly to your device’s circuit board and contains something called “Remote SIM Provisioning,” which allows customers to remotely activate the e-SIM on their devices. Right now, Google’s Pixel 2 and the Apple Watch 3 (along with some cars), are the only real consumer tech using eSIMs, but that’s expected to change quickly.
What’s Stored On A SIM Card?

A SIM card stores an International Mobile Subscriber Identity (IMSI) number, which is a unique 15 digit number identifying the card on carrier’s mobile network. The IMSI is an important part of the lookup process and determines the network to which a mobile device connects.
Along with the IMSI, a 128-bit value authentication key (Ki) is sent to verify your SIM with the GSM cellular network. The Ki is assigned by the operator (MTN UGANDA, AIRTEL, AFRICELL UTL)and stored in a database on their network.
A SIM card is also capable of storing SMS messages and the names and phone numbers of up to 500 contacts, depending on the memory size of the SIM card you have. If you have to change phones for whatever reason, you’re able to transfer your contacts via the SIM card painlessly.
Most SIM cards contain between 64-128 KB of storage.
How Does A SIM Work?
Essentially, a SIM card serves as your phone’s credentials to access the carrier network. Because the SIM holds this information, you’re able to pop it into any phone with the same carrier, or an unlocked phone, to access the network.
Here’s how it works:
- When you boot up your device, it obtains the IMSI from the SIM, and then relays the IMSI to the network in order to request access.
- The operator network searches the database for your IMSI and the associated Ki.
- Assuming your IMSI and Ki are verified, the operator then generates a random number, signs it with your Ki using the GSM cryptography algorithm for computing SRES_2, and creates a new unique number.
- The network then sends that unique number back to the device, which then passes it to the SIM to use in the same algorithm, creating a third number. This number is then relayed back to the network.
- If both numbers match, the SIM card is deemed legitimate and is granted access to the network.
So if you break the screen on your phone, while it’s getting fixed you can take your SIM out and put it in a replacement phone and still access phone calls, texts, and data from your network.
Security
So, what if your phone gets stolen? Can someone just pop out your SIM card and stick it into another phone?
Well, yeah.
Someone could put that card into another phone, and then use it to make calls, which can get quite expensive if it’s used to make premium calls. If your SIM also contains contact or other information, they will have access to that as well. The good news is that most modern phones do not store that kind of information on SIM cards.
Still, the first thing you should do if your phone or SIM card is stolen is report the theft to your carrier. They can then block that SIM card from being used at all.
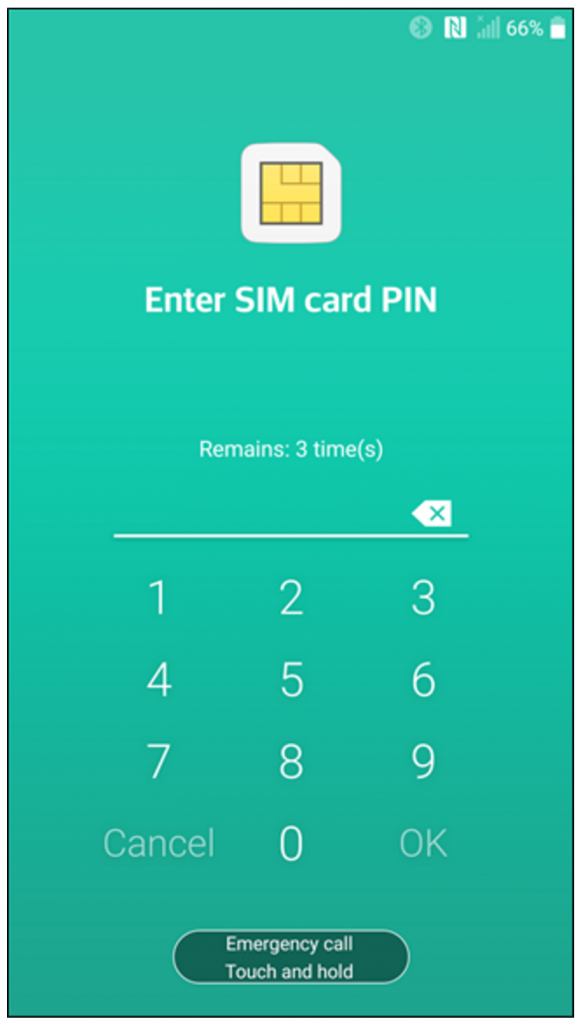
You can also protect your SIM card with its own PIN using the “SIM Lock” feature on your phone. The feature locks the SIM card with a PIN so that the card can’t be used without unlocking it. Even though you set the feature using your phone, the PIN is tied to the SIM card itself. Both Android and iPhone have this feature in the respected settings menu.
With so many SIM cards being actively used, they may just be the most used security token in the world. With your phone number being the key to two-factor authentication, hackers are always trying to figure out ways to get hold of your phone number so they can take control of your email, social media account, and even your bank account. To do this, they use a method called “SIM swapping,” which allows them to take over anything tied to your number. By calling your mobile provider and pretending to be you, they trick the representative into sending a new SIM card to them, gaining complete control.
How do you combat this technique? With another PIN, of course. This time, you just call your carrier and ask them to add a security PIN to your account. That way, anybody who talks to them to make account changes (including you) must provide the PIN number first.
